Service Boundaries That Actually Work: Domain Driven Design in Practice
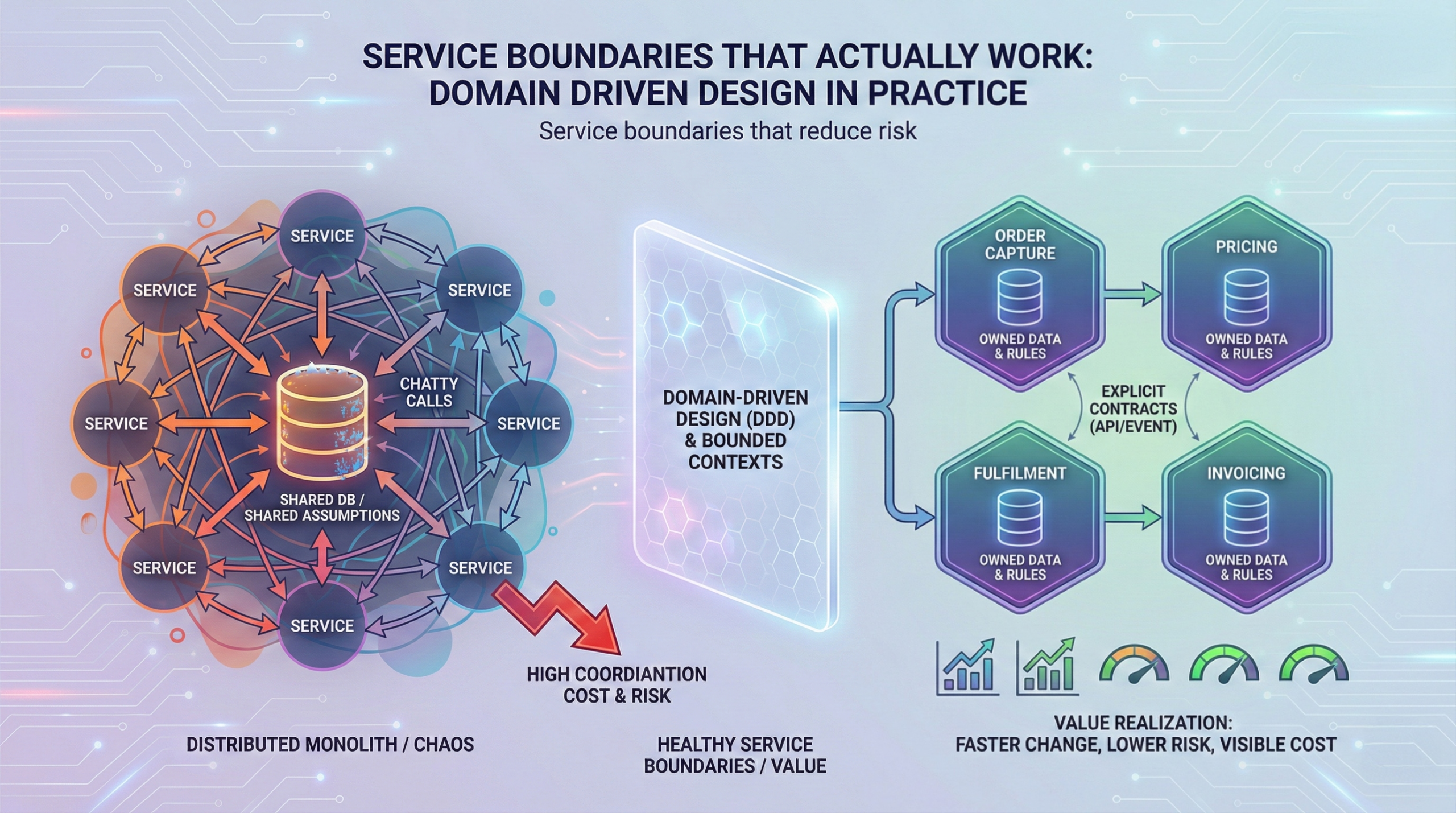
If your microservices programme disappoints, the root cause is often not Kubernetes, CI/CD, or cloud cost. It is service boundaries that do not match how the business actually works. When you slice a monolith the wrong way, you create a distributed monolith: more deployments, more integrations, and more incidents, with little agility to show for it.
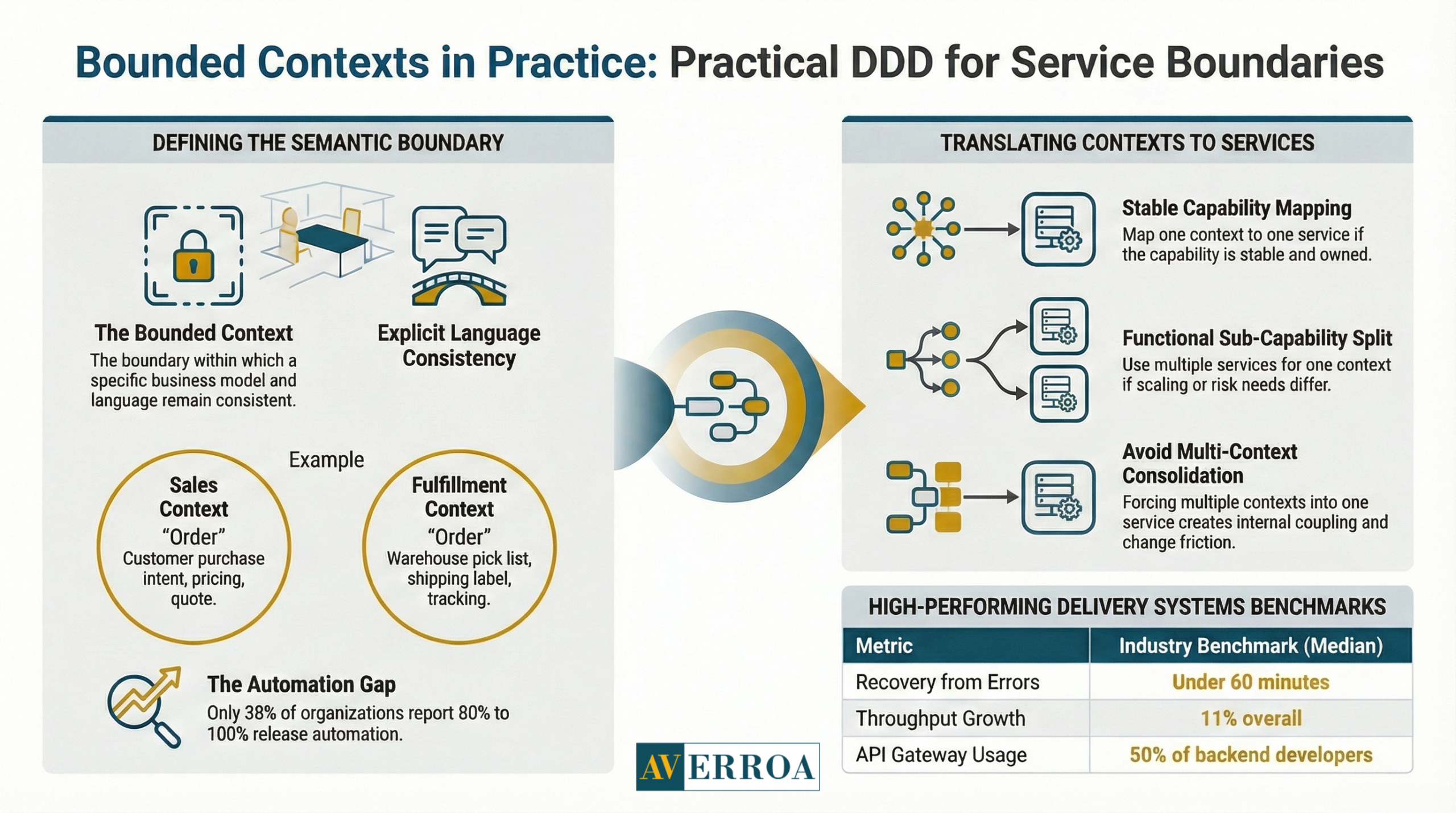
This matters now because microservices are mainstream. CNCF and SlashData report that 46% of backend developers are operating microservices and 50% use API gateways, which means more organisations are betting their delivery model on distributed systems. At the same time, delivery expectations keep rising. CircleCI reports throughput is up 11% overall and 68% on production branches, and median recovery from errors is under 60 minutes. Those numbers set an implicit bar for how quickly teams must change and stabilise systems.
Domain Driven Design helps because it gives a practical way to define service boundaries around business meaning, not around database tables or org charts. Martin Fowler’s definition of a bounded context is still the cleanest starting point.
Service boundaries decide whether microservices pay back
Executives tend to ask whether microservices will speed up delivery or reduce risk. The more accurate question is this: do we have service boundaries that allow independent change without breaking customer journeys?
A microservice only buys you autonomy if it aligns with a cohesive business capability and has a stable contract with the rest of the estate. If not, you get “microservices theatre”: lots of repositories and deployment pipelines, but constant cross team coordination.
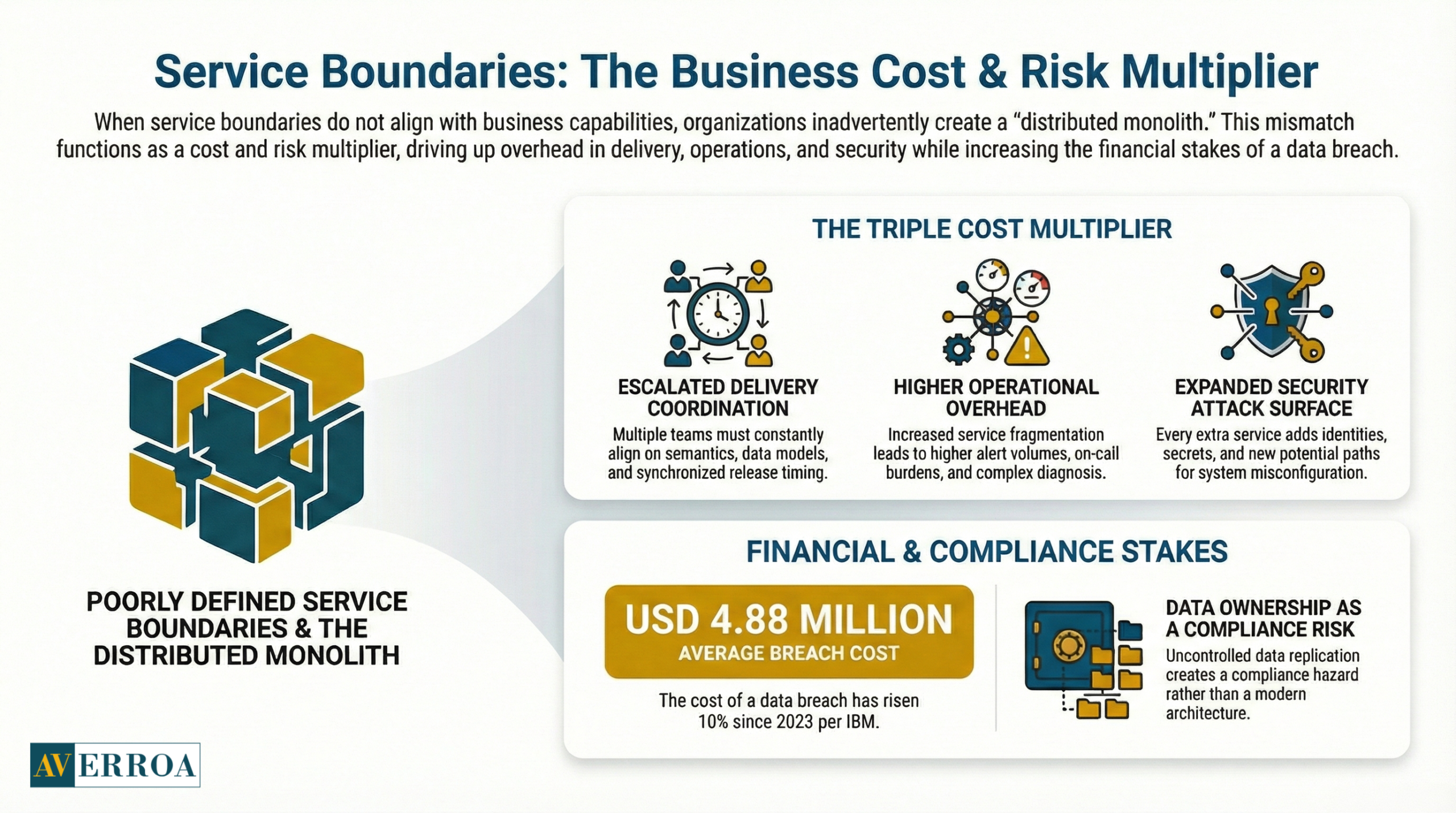
Business impact and risk: boundaries are a cost and risk multiplier
Bad service boundaries increase three costs at once.
First, they increase delivery coordination cost. Each change requires multiple teams to agree on semantics, data, and release timing.
Second, they increase operational cost. More services mean more alerts, more on call load, and more partial failures to diagnose.
Third, they increase security and compliance exposure. Every extra service adds identities, secrets, policy configuration, and potential misconfiguration paths.
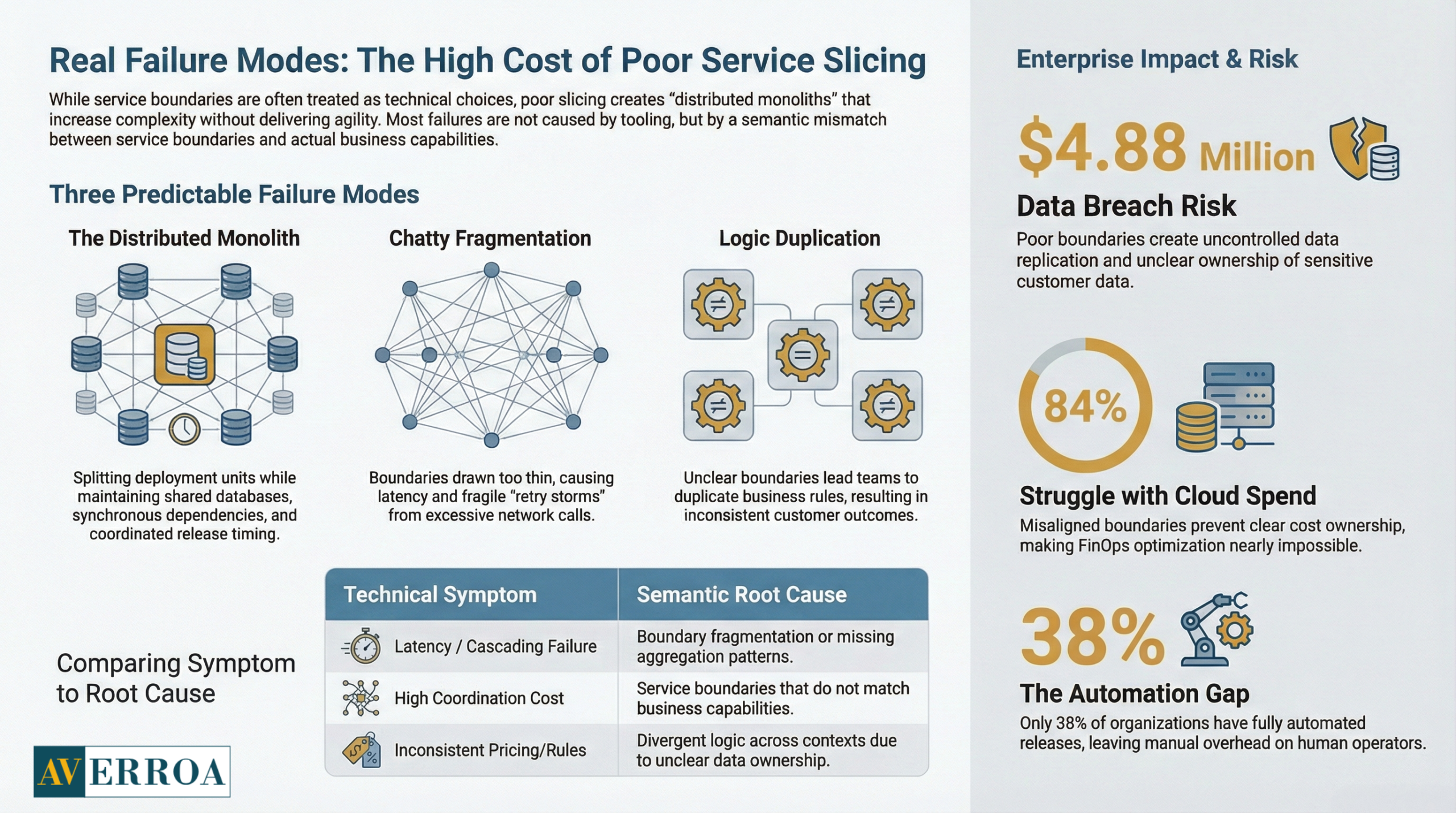
This becomes financially meaningful fast. IBM’s Cost of a Data Breach Report 2024 puts the average total cost of a breach at USD 4.88 million, up 10% from 2023. If your boundaries create uncontrolled data replication or unclear ownership of sensitive data, you have created a compliance risk, not a modern architecture.
Operating model and governance: service boundaries require decision rights
Healthy service boundaries imply ownership. Ownership implies governance changes.
A workable enterprise rule set looks traditional in spirit, but modern in execution:
- One accountable owner per bounded business capability, including service reliability outcomes.
- Architecture guardrails that are automated, not debated per change.
- A clear exception process, because enterprise reality is messy.
CNCF’s Annual Survey 2024 shows organisations are still closing the automation gap. Only 38% reported 80% to 100% of releases are automated, while the organisational average automation level was 59.2% in 2024. The implication is blunt: if your automation and governance are not mature, the overhead of many services will land on humans, and your delivery system will slow down.
Bounded contexts in practice: Domain Driven Design without the academic overload
Domain Driven Design is often presented as vocabulary and diagrams. Executives need it as a decision tool for service boundaries.
What a bounded context is, in plain terms
Martin Fowler describes a bounded context as a central DDD pattern that divides large models and teams and makes the relationships between contexts explicit. Put simply: a bounded context is the boundary within which a particular business model and language are consistent.
Inside a bounded context, “customer”, “order”, or “case” has a specific meaning. Across contexts, the same word can mean something different, and that is normal. What matters is that the difference is explicit.
Fowler’s microservices article links this directly to service design: bounded contexts help you think about how to divide a complex domain into components, whether you deploy them as a monolith or as services.
How bounded contexts translate into service boundaries
A bounded context is not automatically a microservice. In practice, you usually start with bounded contexts, then decide which contexts justify independent deployment and ownership.
A practical translation for enterprise architects:
- One bounded context can map to one service, if the capability is stable and the team can own it end to end.
- One bounded context can map to a small set of services, if there are clear sub capabilities with different scaling, risk, or release needs.
- Multiple bounded contexts should not be forced into one service if the business language conflicts, because you will create internal coupling and constant change friction.
Architecture and integration implications: contracts matter more than code
Once you set service boundaries, you need explicit integration contracts:
- APIs that reflect business outcomes, not database CRUD.
- Event contracts for state changes that other domains care about.
- Clear data ownership and rules for read access, caching, and reporting.
Observability becomes a boundary discipline as well. Grafana’s 2025 Observability Survey reports 67% use Prometheus in production, and OpenTelemetry production usage is 41%, with 38% investigating or building POCs. The implication is that distributed systems tooling is standardising, but adoption is still uneven. If your service boundaries increase cross service calls, you must standardise tracing and correlation, or your incident triage cost will rise.
Real failure modes of poor service slicing
Bad service boundaries fail in predictable ways. The symptoms look “technical”, but the cause is almost always semantic mismatch.
Failure mode 1: the “distributed monolith”
You split deployment units, but keep shared assumptions:
- A shared database schema that multiple services write to.
- Synchronous calls on the critical path for every transaction.
- Shared release timing because one service cannot change without another.
Result: more moving parts, same coupling. This is why executives feel microservices “did not deliver”.
Anonymised example: an EU industrial firm split an ERP adjacent monolith into services by technical layers: UI service, business logic service, data service. It looked modern, but every change required all three deployments and cross service debugging. The fix was to redefine service boundaries by business capability: pricing, order capture, fulfilment, invoicing, each with its own data ownership rules.
Failure mode 2: chatty services and latency inflation
If boundaries are drawn too thin, you get excessive network calls. This creates latency, cascading failures, and fragile retry storms.
A quick test: if a single user journey regularly triggers more than 20 cross service calls in the steady state, you probably have boundary fragmentation or missing aggregation patterns such as BFFs and read models.
Failure mode 3: duplicate business rules and inconsistent outcomes
When service boundaries are unclear, teams duplicate “simple rules” across services. Over time, the rules diverge. Customer outcomes become inconsistent, which is an executive level quality issue, not a developer inconvenience.
Anonymised example: a MENA retail platform had separate “discount” logic in checkout, promotions, and customer service tooling. Refund disputes increased because each system computed eligibility differently. They resolved it by moving discount policy into one bounded context with a clear contract, then treating other systems as consumers.
Failure mode 4: “context drift” under organisational pressure
Conway’s Law is practical: architecture follows communication structure. If teams are organised around functions, boundaries drift toward shared platforms and shared schemas.
DORA’s 2024 research is based on a global survey of over 39,000 professionals. The managerial implication is that you cannot “architect away” organisational constraints. You need an operating model that supports ownership and alignment, or your service boundaries will degrade.
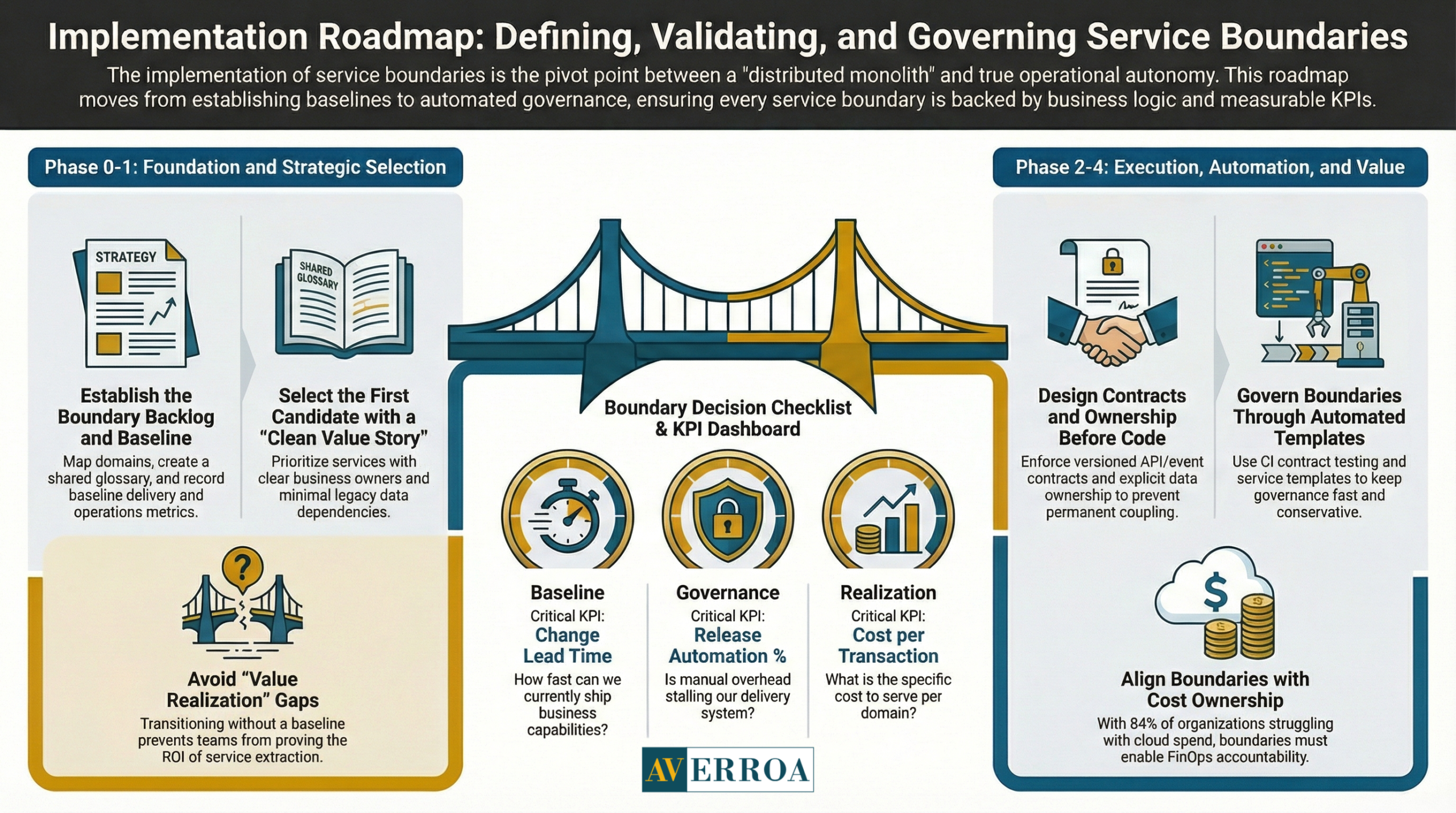
Implementation approach: defining, validating, and governing service boundaries
The implementation approach is where organisations either institutionalise good boundaries or hard code bad ones.
Phase 0: establish the boundary backlog and baseline KPIs
Deliverables:
- A domain map with candidate bounded contexts and a shared glossary.
- A context relationship view, who depends on whom and why.
- A baseline of delivery and ops metrics for the current monolith.
Suggested KPIs:
- Change lead time and deployment frequency, per business capability.
- Change failure rate and mean time to recover.
- Number of cross team handoffs per change request.
- Production incident recurrence rate by domain.
Use CircleCI’s 2024 recovery and throughput benchmarks as directional context for what “good” can look like when delivery systems are disciplined.
Typical failure mode: teams begin extracting services with no baseline, then cannot prove value realisation and cannot prioritise the next slice.
Phase 1: pick the first bounded context with a clean value story
A good first candidate has:
- Clear business owner and measurable business outcome.
- Limited dependency on legacy data, or an agreed read strategy.
- A small number of upstream and downstream integrations.
In workflow heavy enterprises, common candidates are notifications, document generation, identity and access wrappers, or a discrete workflow step that can be routed independently.
Phase 2: design contracts and data ownership before code
This is where service boundaries become enforceable.
Guardrails:
- API and event contracts are versioned.
- Data ownership is explicit, including PII.
- Cross boundary data access is via contract, not via shared tables.
- Observability is mandatory, logs, metrics, traces, correlation IDs.
Grafana’s survey numbers are useful here. If you want microservices benefits, tracing coverage cannot be optional as call chains grow.
Typical failure mode: teams agree on “temporary” shared database access, then it becomes permanent.
Phase 3: govern boundaries through templates and automation
Your governance should feel conservative, because it protects the enterprise, but it should execute automatically so it does not slow delivery.
CNCF’s automation gap data is the warning light. If your releases are not mostly automated, governance work will land as manual overhead and programmes will stall.
Practical governance mechanisms:
- Service templates with standard telemetry, security scanning, and deploy pipelines.
- Contract testing in CI to prevent accidental breaking changes.
- A lightweight architecture forum focused on boundary disputes, not on approving every design.
Phase 4: measure value realisation and cost to serve per boundary
Microservices often increase cloud cost before they reduce it, because you run old and new in parallel.
Flexera’s 2025 findings show the scale of the cost challenge: 84% of organisations struggle to manage cloud spend, cloud spend is expected to increase by 28% in the coming year, and 59% report an active FinOps practice. The implication is that your service boundaries must align with cost ownership. If no one owns the cost per domain, you cannot optimise it.
Value realisation KPIs that executives will recognise:
- Cost per transaction or per workflow step, by bounded context.
- Time to change a policy or workflow rule, end to end.
- Incident volume and severity for the migrated context.
- Audit finding rate and evidence production time.
Actionable Takeaways
- Treat service boundaries as a business decision about ownership, risk, and speed, not a technical refactor.
- Start with bounded contexts to stabilise business meaning, then decide which contexts justify independent deployment.
- Avoid “distributed monolith” outcomes by enforcing data ownership and integration contracts.
- Make observability a boundary gate, because tracing coverage becomes critical as cross service calls grow.
- Use automation and templates to keep governance conservative in intent but fast in execution.
- Expect cost pressure during migration, and assign cost ownership per bounded context so optimisation is possible.
- Measure value by time to change, reliability, and cost to serve, not by number of services.
- If boundaries are disputed weekly, pause extraction and invest in domain mapping and shared language.
If you are modernising workflow heavy enterprise systems and want boundary definition tied to delivery and measurable outcomes, explore Enterprise workflow automation and use it as the anchor for domain mapping, contract design, and controlled implementation.
References
- CNCF + SlashData State of Cloud Native Development Q3 2025 (PDF, Nov 2025) → https://www.cncf.io/wp-content/uploads/2025/11/cncf_report_stateofcloud_111025a.pdf
- CNCF announcement on microservices and API gateway adoption (Nov 11, 2025) → https://www.cncf.io/announcements/2025/11/11/cncf-and-slashdata-survey-finds-cloud-native-ecosystem-surges-to-15-6m-developers/
- CNCF Annual Survey 2024 report (PDF, Apr 2025) → https://www.cncf.io/wp-content/uploads/2025/04/cncf_annual_survey24_031225a.pdf
- Grafana Observability Survey 2025 key findings (2025) → https://grafana.com/observability-survey/2025/
- CircleCI State of Software Delivery 2024 (PDF, 2024) → https://circleci.com/landing-pages/assets/CircleCI-The-2024-State-of-Software-Delivery.pdf
- Flexera press release on cloud spend challenges (Mar 19, 2025) → https://www.flexera.com/about-us/press-center/new-flexera-report-finds-84-percent-of-organizations-struggle-to-manage-cloud-spend
- IBM Cost of a Data Breach Report 2024 (PDF, Jul 2024) → https://wp.table.media/wp-content/uploads/2024/07/30132828/Cost-of-a-Data-Breach-Report-2024.pdf
- Martin Fowler, Bounded Context (Jan 15, 2014) → https://www.martinfowler.com/bliki/BoundedContext.html
Service Boundaries That Actually Work: Domain Driven Design in Practice
If your microservices programme disappoints, the root cause is often not Kubernetes, CI/CD, or cloud cost. It is service boundaries that do not match how the business actually works. When you slice a monolith the wrong way, you create a distributed monolith: more deployments, more integrations, and more incidents, with little agility to show for it.
This matters now because microservices are mainstream. CNCF and SlashData report that 46% of backend developers are operating microservices and 50% use API gateways, which means more organisations are betting their delivery model on distributed systems. At the same time, delivery expectations keep rising. CircleCI reports throughput is up 11% overall and 68% on production branches, and median recovery from errors is under 60 minutes. Those numbers set an implicit bar for how quickly teams must change and stabilise systems.
Domain Driven Design helps because it gives a practical way to define service boundaries around business meaning, not around database tables or org charts. Martin Fowler’s definition of a bounded context is still the cleanest starting point.
Service boundaries decide whether microservices pay back
Executives tend to ask whether microservices will speed up delivery or reduce risk. The more accurate question is this: do we have service boundaries that allow independent change without breaking customer journeys?
A microservice only buys you autonomy if it aligns with a cohesive business capability and has a stable contract with the rest of the estate. If not, you get “microservices theatre”: lots of repositories and deployment pipelines, but constant cross team coordination.
Business impact and risk: boundaries are a cost and risk multiplier
Bad service boundaries increase three costs at once.
First, they increase delivery coordination cost. Each change requires multiple teams to agree on semantics, data, and release timing.
Second, they increase operational cost. More services mean more alerts, more on call load, and more partial failures to diagnose.
Third, they increase security and compliance exposure. Every extra service adds identities, secrets, policy configuration, and potential misconfiguration paths.
This becomes financially meaningful fast. IBM’s Cost of a Data Breach Report 2024 puts the average total cost of a breach at USD 4.88 million, up 10% from 2023. If your boundaries create uncontrolled data replication or unclear ownership of sensitive data, you have created a compliance risk, not a modern architecture.
Operating model and governance: service boundaries require decision rights
Healthy service boundaries imply ownership. Ownership implies governance changes.
A workable enterprise rule set looks traditional in spirit, but modern in execution:
- One accountable owner per bounded business capability, including service reliability outcomes.
- Architecture guardrails that are automated, not debated per change.
- A clear exception process, because enterprise reality is messy.
CNCF’s Annual Survey 2024 shows organisations are still closing the automation gap. Only 38% reported 80% to 100% of releases are automated, while the organisational average automation level was 59.2% in 2024. The implication is blunt: if your automation and governance are not mature, the overhead of many services will land on humans, and your delivery system will slow down.
Bounded contexts in practice: Domain Driven Design without the academic overload
Domain Driven Design is often presented as vocabulary and diagrams. Executives need it as a decision tool for service boundaries.
What a bounded context is, in plain terms
Martin Fowler describes a bounded context as a central DDD pattern that divides large models and teams and makes the relationships between contexts explicit. Put simply: a bounded context is the boundary within which a particular business model and language are consistent.
Inside a bounded context, “customer”, “order”, or “case” has a specific meaning. Across contexts, the same word can mean something different, and that is normal. What matters is that the difference is explicit.
Fowler’s microservices article links this directly to service design: bounded contexts help you think about how to divide a complex domain into components, whether you deploy them as a monolith or as services.
How bounded contexts translate into service boundaries
A bounded context is not automatically a microservice. In practice, you usually start with bounded contexts, then decide which contexts justify independent deployment and ownership.
A practical translation for enterprise architects:
- One bounded context can map to one service, if the capability is stable and the team can own it end to end.
- One bounded context can map to a small set of services, if there are clear sub capabilities with different scaling, risk, or release needs.
- Multiple bounded contexts should not be forced into one service if the business language conflicts, because you will create internal coupling and constant change friction.
Architecture and integration implications: contracts matter more than code
Once you set service boundaries, you need explicit integration contracts:
- APIs that reflect business outcomes, not database CRUD.
- Event contracts for state changes that other domains care about.
- Clear data ownership and rules for read access, caching, and reporting.
Observability becomes a boundary discipline as well. Grafana’s 2025 Observability Survey reports 67% use Prometheus in production, and OpenTelemetry production usage is 41%, with 38% investigating or building POCs. The implication is that distributed systems tooling is standardising, but adoption is still uneven. If your service boundaries increase cross service calls, you must standardise tracing and correlation, or your incident triage cost will rise.
Real failure modes of poor service slicing
Bad service boundaries fail in predictable ways. The symptoms look “technical”, but the cause is almost always semantic mismatch.
Failure mode 1: the “distributed monolith”
You split deployment units, but keep shared assumptions:
- A shared database schema that multiple services write to.
- Synchronous calls on the critical path for every transaction.
- Shared release timing because one service cannot change without another.
Result: more moving parts, same coupling. This is why executives feel microservices “did not deliver”.
Anonymised example: an EU industrial firm split an ERP adjacent monolith into services by technical layers: UI service, business logic service, data service. It looked modern, but every change required all three deployments and cross service debugging. The fix was to redefine service boundaries by business capability: pricing, order capture, fulfilment, invoicing, each with its own data ownership rules.
Failure mode 2: chatty services and latency inflation
If boundaries are drawn too thin, you get excessive network calls. This creates latency, cascading failures, and fragile retry storms.
A quick test: if a single user journey regularly triggers more than 20 cross service calls in the steady state, you probably have boundary fragmentation or missing aggregation patterns such as BFFs and read models.
Failure mode 3: duplicate business rules and inconsistent outcomes
When service boundaries are unclear, teams duplicate “simple rules” across services. Over time, the rules diverge. Customer outcomes become inconsistent, which is an executive level quality issue, not a developer inconvenience.
Anonymised example: a MENA retail platform had separate “discount” logic in checkout, promotions, and customer service tooling. Refund disputes increased because each system computed eligibility differently. They resolved it by moving discount policy into one bounded context with a clear contract, then treating other systems as consumers.
Failure mode 4: “context drift” under organisational pressure
Conway’s Law is practical: architecture follows communication structure. If teams are organised around functions, boundaries drift toward shared platforms and shared schemas.
DORA’s 2024 research is based on a global survey of over 39,000 professionals. The managerial implication is that you cannot “architect away” organisational constraints. You need an operating model that supports ownership and alignment, or your service boundaries will degrade.
Implementation approach: defining, validating, and governing service boundaries
The implementation approach is where organisations either institutionalise good boundaries or hard code bad ones.
Phase 0: establish the boundary backlog and baseline KPIs
Deliverables:
- A domain map with candidate bounded contexts and a shared glossary.
- A context relationship view, who depends on whom and why.
- A baseline of delivery and ops metrics for the current monolith.
Suggested KPIs:
- Change lead time and deployment frequency, per business capability.
- Change failure rate and mean time to recover.
- Number of cross team handoffs per change request.
- Production incident recurrence rate by domain.
Use CircleCI’s 2024 recovery and throughput benchmarks as directional context for what “good” can look like when delivery systems are disciplined.
Typical failure mode: teams begin extracting services with no baseline, then cannot prove value realisation and cannot prioritise the next slice.
Phase 1: pick the first bounded context with a clean value story
A good first candidate has:
- Clear business owner and measurable business outcome.
- Limited dependency on legacy data, or an agreed read strategy.
- A small number of upstream and downstream integrations.
In workflow heavy enterprises, common candidates are notifications, document generation, identity and access wrappers, or a discrete workflow step that can be routed independently.
Phase 2: design contracts and data ownership before code
This is where service boundaries become enforceable.
Guardrails:
- API and event contracts are versioned.
- Data ownership is explicit, including PII.
- Cross boundary data access is via contract, not via shared tables.
- Observability is mandatory, logs, metrics, traces, correlation IDs.
Grafana’s survey numbers are useful here. If you want microservices benefits, tracing coverage cannot be optional as call chains grow.
Typical failure mode: teams agree on “temporary” shared database access, then it becomes permanent.
Phase 3: govern boundaries through templates and automation
Your governance should feel conservative, because it protects the enterprise, but it should execute automatically so it does not slow delivery.
CNCF’s automation gap data is the warning light. If your releases are not mostly automated, governance work will land as manual overhead and programmes will stall.
Practical governance mechanisms:
- Service templates with standard telemetry, security scanning, and deploy pipelines.
- Contract testing in CI to prevent accidental breaking changes.
- A lightweight architecture forum focused on boundary disputes, not on approving every design.
Phase 4: measure value realisation and cost to serve per boundary
Microservices often increase cloud cost before they reduce it, because you run old and new in parallel.
Flexera’s 2025 findings show the scale of the cost challenge: 84% of organisations struggle to manage cloud spend, cloud spend is expected to increase by 28% in the coming year, and 59% report an active FinOps practice. The implication is that your service boundaries must align with cost ownership. If no one owns the cost per domain, you cannot optimise it.
Value realisation KPIs that executives will recognise:
- Cost per transaction or per workflow step, by bounded context.
- Time to change a policy or workflow rule, end to end.
- Incident volume and severity for the migrated context.
- Audit finding rate and evidence production time.
Actionable Takeaways
- Treat service boundaries as a business decision about ownership, risk, and speed, not a technical refactor.
- Start with bounded contexts to stabilise business meaning, then decide which contexts justify independent deployment.
- Avoid “distributed monolith” outcomes by enforcing data ownership and integration contracts.
- Make observability a boundary gate, because tracing coverage becomes critical as cross service calls grow.
- Use automation and templates to keep governance conservative in intent but fast in execution.
- Expect cost pressure during migration, and assign cost ownership per bounded context so optimisation is possible.
- Measure value by time to change, reliability, and cost to serve, not by number of services.
- If boundaries are disputed weekly, pause extraction and invest in domain mapping and shared language.
If you are modernising workflow heavy enterprise systems and want boundary definition tied to delivery and measurable outcomes, explore Enterprise workflow automation and use it as the anchor for domain mapping, contract design, and controlled implementation.
References
- CNCF + SlashData State of Cloud Native Development Q3 2025 (PDF, Nov 2025) → https://www.cncf.io/wp-content/uploads/2025/11/cncf_report_stateofcloud_111025a.pdf
- CNCF announcement on microservices and API gateway adoption (Nov 11, 2025) → https://www.cncf.io/announcements/2025/11/11/cncf-and-slashdata-survey-finds-cloud-native-ecosystem-surges-to-15-6m-developers/
- CNCF Annual Survey 2024 report (PDF, Apr 2025) → https://www.cncf.io/wp-content/uploads/2025/04/cncf_annual_survey24_031225a.pdf
- Grafana Observability Survey 2025 key findings (2025) → https://grafana.com/observability-survey/2025/
- CircleCI State of Software Delivery 2024 (PDF, 2024) → https://circleci.com/landing-pages/assets/CircleCI-The-2024-State-of-Software-Delivery.pdf
- Flexera press release on cloud spend challenges (Mar 19, 2025) → https://www.flexera.com/about-us/press-center/new-flexera-report-finds-84-percent-of-organizations-struggle-to-manage-cloud-spend
- IBM Cost of a Data Breach Report 2024 (PDF, Jul 2024) → https://wp.table.media/wp-content/uploads/2024/07/30132828/Cost-of-a-Data-Breach-Report-2024.pdf
- Martin Fowler, Bounded Context (Jan 15, 2014) → https://www.martinfowler.com/bliki/BoundedContext.html
Meet The Author
Meet The Author
Senior software engineer focused on backend systems and Android apps, delivering scalable web/mobile/cloud solutions. Leads technical direction, mentors teams, and ships high-performance services using ASP.NET Core/C#, microservices, and cloud-native infrastructure.
Senior software engineer focused on backend systems and Android apps, delivering scalable web/mobile/cloud solutions. Leads technical direction, mentors teams, and ships high-performance services using ASP.NET Core/C#, microservices, and cloud-native infrastructure.
Averroa Principal
Table of content
- Service Boundaries That Actually Work: Domain Driven Design in Practice
- Service boundaries decide whether microservices pay back
- Business impact and risk: boundaries are a cost and risk multiplier
- Operating model and governance: service boundaries require decision rights
- Bounded contexts in practice: Domain Driven Design without the academic overload
- Real failure modes of poor service slicing
- Implementation approach: defining, validating, and governing service boundaries
- Phase 0: establish the boundary backlog and baseline KPIs
- Phase 1: pick the first bounded context with a clean value story
- Phase 2: design contracts and data ownership before code
- Phase 3: govern boundaries through templates and automation
- Phase 4: measure value realisation and cost to serve per boundary
- Actionable Takeaways
- References
- Meet The Author