Should You Migrate at All? A Decision Framework for Monolith vs Microservices
“Move to microservices” has become a default recommendation in many enterprise roadmaps. In practice, the monolith vs microservices decision is not a style choice. It is a capital allocation decision with operational consequences. The timing matters because the external pressure is rising while delivery capacity is not. Cloud costs are climbing and cost governance is now front page for many CIOs. Flexera’s 2025 State of the Cloud release found 84% of organisations cite managing cloud spend as the top cloud challenge, with cloud spend expected to increase by 28% in the coming year. At the same time, regulators are tightening expectations on resilience and incident handling. The EU NIS2 transposition deadline was 17 October 2024, and the Commission is already proposing targeted amendments in January 2026 to simplify compliance. DORA entered into application on 17 January 2025 for financial entities.
Against that backdrop, microservices can be the right move, but only when the business context justifies the additional operating model, security, and platform overhead. This article gives a practical, executive friendly framework to decide, before you commit your organisation to a multi year migration.
Start with the real question: what problem are you trying to buy down?
A useful way to de risk the monolith vs microservices debate is to translate it into business problems you are willing to pay to solve. Microservices are not “better architecture”. They are a specific operating model for building and running software at scale.
In board terms, you pay for microservices with complexity, then you earn it back with speed, resilience, and organisational autonomy. If you cannot articulate where the payback shows up on your P and L or your risk register, the safest default is to improve the monolith.
Three signals that the “do nothing” option is getting more expensive:
- Cloud and platform economics are now a constraint. Flexera reports cloud spend is expected to rise 28% and budgets already exceed limits by 17% in many organisations. If you split a system into services without disciplined FinOps and platform standards, cost tends to sprawl rather than shrink.
- Security and resilience are becoming measurable obligations. IBM’s 2024 Cost of a Data Breach report put the global average breach cost at USD 4.88m, with the Middle East sample at USD 8.75m. Microservices change your attack surface, identity model, and incident blast radius. That can help or hurt, depending on governance.
- The market has normalised cloud native patterns. The CNCF Annual Survey (March 2025) reports 89% cloud native adoption, 91% of organisations using containers in production, and Kubernetes used, piloted, or evaluated by 93% of companies. In other words, the ecosystem is mature, but maturity does not remove the need for good judgement.
The decision framework below is designed to be used in portfolio governance, not as a technical beauty contest.
Monolith vs microservices: a decision framework you can score
I recommend a simple scoring model across seven dimensions. Use a 0 to 2 score for each. Total out of 14.
- 0 means monolith friendly
- 1 means ambiguous, proceed selectively
- 2 means microservices likely justified
1) Change volatility and release independence
Ask: do different parts of the system change at different rates, driven by different business owners?
A monolith is efficient when most changes are coordinated anyway. Microservices pay off when you have truly independent release trains. If every release still needs a cross domain steering committee, microservices will not produce speed, it will produce meetings.
Evidence context: microservices are widely adopted in the developer community, but adoption alone does not prove suitability. SlashData for CNCF (October 2025) reports microservices are used by 46% of backend developers and API gateways by 50%. Many of those implementations are supported by platform teams that hide complexity. If you do not have that platform maturity, independence is harder to achieve.
Score guidance:
- 0: mostly coordinated releases
- 1: some components could be independent
- 2: clear product domains with separate backlogs and KPIs
2) Scaling profile and performance hotspots
Ask: do you have uneven load, or a few services that need to scale differently?
Microservices make sense when scaling is asymmetric. If the whole system scales together, a well tuned monolith can be cheaper and simpler.
Score guidance:
- 0: uniform scaling, predictable load
- 1: a few hotspots, could be isolated with caching or modularisation
- 2: clearly separable workloads, spiky demand, different SLOs
3) Team topology and operational capacity
Ask: do you have the people to run distributed systems, not just build them?
This is where many programmes fail. Microservices require always on operational ownership, observability, SRE practices, and strong runbooks. Otherwise, you get a distributed monolith with slower delivery.
CNCF’s 2024 survey highlights containers in production are common, but deployment is “challenged primarily by cultural changes in the development team”. That cultural point is the real cost driver.
Score guidance:
- 0: one or two teams, limited 24 by 7 coverage
- 1: multiple teams, partial ownership, some on call maturity
- 2: several stable product teams, defined on call, incident process, platform support
4) Regulatory pressure and auditability
Ask: do you need stronger operational resilience, traceability, and third party controls?
For EU and many cross border firms, the baseline has moved. NIS2 required transposition by 17 October 2024 and repealed NIS1 from 18 October 2024. For financial entities, DORA entered into application on 17 January 2025 and explicitly covers ICT risk management, third party risk, resilience testing, and incident reporting.
Microservices can improve auditability if you standardise logging, identity, and change control. They can also create audit chaos if every team invents its own approach.
Score guidance:
- 0: minimal regulatory constraints
- 1: some compliance needs, manageable with monolith controls
- 2: high resilience and reporting expectations, complex third party ecosystem
5) Integration landscape and data ownership
Ask: are you integrating with many systems, and do you have a clear data model?
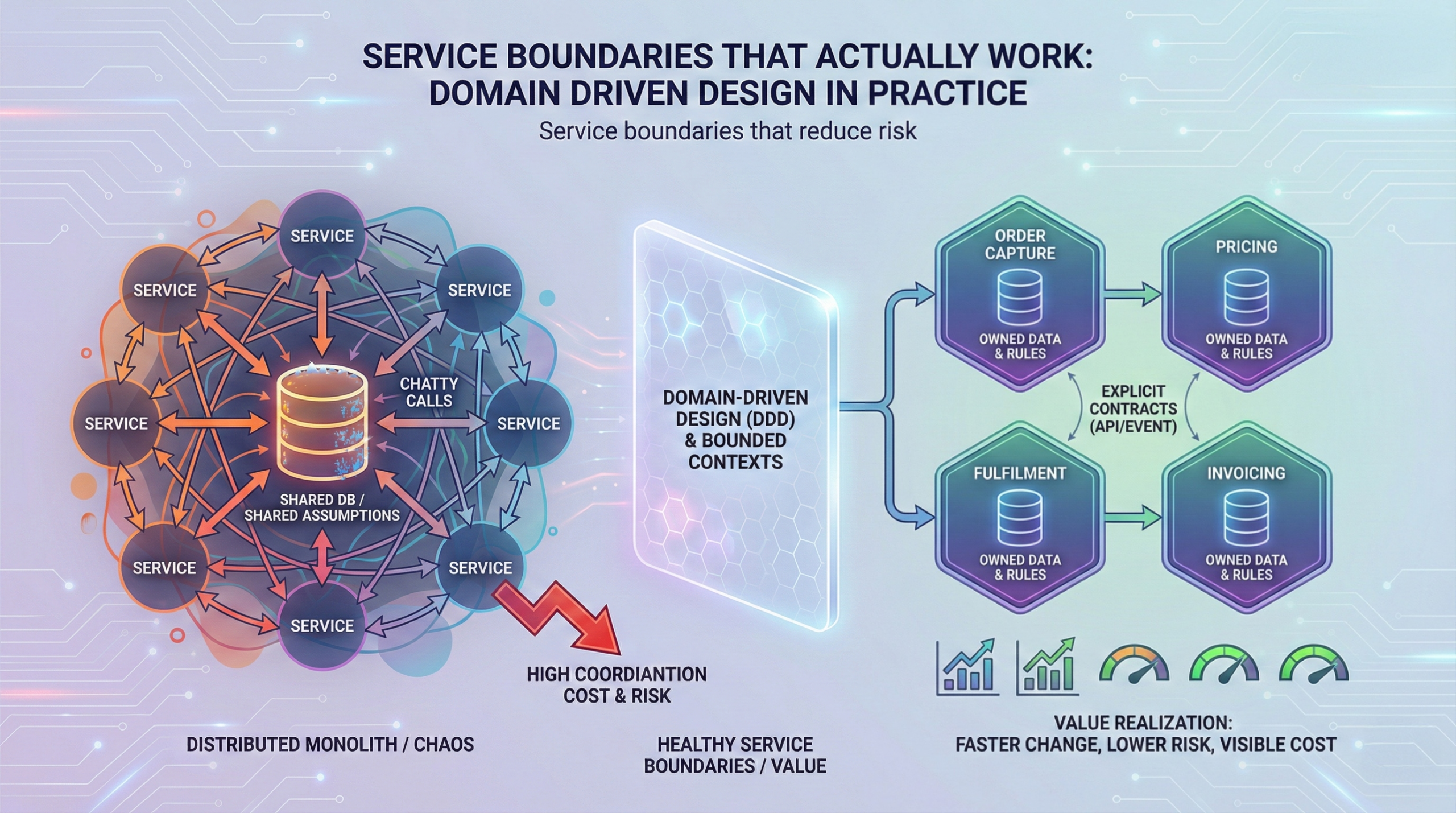
Microservices are a data architecture decision as much as an application decision. If you cannot define bounded contexts and data ownership, you will create distributed transactions, duplicated data, and inconsistent reporting.
Gartner warns that cloud adoption success is not guaranteed. It predicts 25% of organisations will experience significant dissatisfaction with cloud adoption by 2028 due to unrealistic expectations, suboptimal implementation, or uncontrolled costs. Integration and data sprawl are common root causes.
Score guidance:
- 0: simple integrations, single dominant data model
- 1: moderate complexity, needs API discipline
- 2: many systems, frequent integration change, strong need for domain boundaries
6) Security model and blast radius management
Ask: will microservices reduce or increase your risk?
IBM’s breach cost data is a reminder that the downside is material, especially in MENA where the 2024 Middle East average was USD 8.75m. Microservices can reduce blast radius if you enforce zero trust service identity, segmentation, and least privilege. They increase risk if you multiply endpoints without consistent controls.
Score guidance:
- 0: security controls are ad hoc today
- 1: some standardisation exists, gaps remain
- 2: strong IAM, secrets management, threat modelling, security testing pipelines
7) Platform and cost governance readiness
Ask: do you have a paved road?
Flexera reports 59% are expanding FinOps teams and 60% are using managed service providers to regain control of spend. That is not a coincidence. Microservices without FinOps and platform engineering is a fast route to cost surprises.
Score guidance:
- 0: no shared platform, limited observability, unclear cost allocation
- 1: partial platform, some shared tooling
- 2: internal developer platform or strong shared platform patterns, unit cost visibility
How to interpret the score
- 0 to 5: default to monolith improvement and modularisation
- 6 to 9: selective decomposition for the highest value domains
- 10 to 14: microservices can be justified, plan it as an operating model shift
What changes when you choose microservices: operating model, governance, and architecture
A monolith vs microservices decision changes how work moves through your organisation. Executives should ask for an explicit operating model plan, not just a target architecture diagram.
Operating model and governance changes
Key shifts:
- From project delivery to product ownership. Microservices work best when teams own services end to end, including run and improve.
- From central approvals to guardrails. Governance must move from manual gates to automated policy in pipelines, plus clear standards.
- From shared release management to service level accountability. Teams commit to SLOs and incident response, not just feature delivery.
Practical guardrails that prevent “microservices theatre”:
- Standard service templates (logging, metrics, tracing, health checks, security headers)
- Standard CI and CD patterns with mandatory checks
- Defined API lifecycle and versioning rules
- Centralised identity patterns for service to service access
- A clear exception process, measured and time boxed
Architecture and integration implications (systems, data, security)
Microservices raise three architectural obligations:
- API strategy becomes your integration contract. API gateways are popular for a reason. SlashData reports 50% of backend developers use API gateways. You need consistent routing, auth, throttling, and observability. Otherwise, consumers will break.
- Data must be owned, not shared casually. Shared databases recreate monolith coupling with worse failure modes. Prefer service owned schemas and event driven integration where it fits.
- Security must be uniform. Identity, secrets, encryption, and logging must be consistent. DORA’s focus on ICT risk management and third party oversight is a useful benchmark even outside finance.
Anonymised example: regulated EU group platform
A regulated EU group ran a core workflow platform that supported onboarding and case management. They wanted microservices because competitors were “moving faster”. A first scoring exercise showed only two domains had genuinely independent change cycles. The early win was not microservices. It was a modular monolith refactor plus a single carve out for the document processing domain, driven by scaling hotspots and vendor integration. That produced faster releases without expanding the audit scope across dozens of services.
Implementation approach: phases, guardrails, failure modes, and KPIs
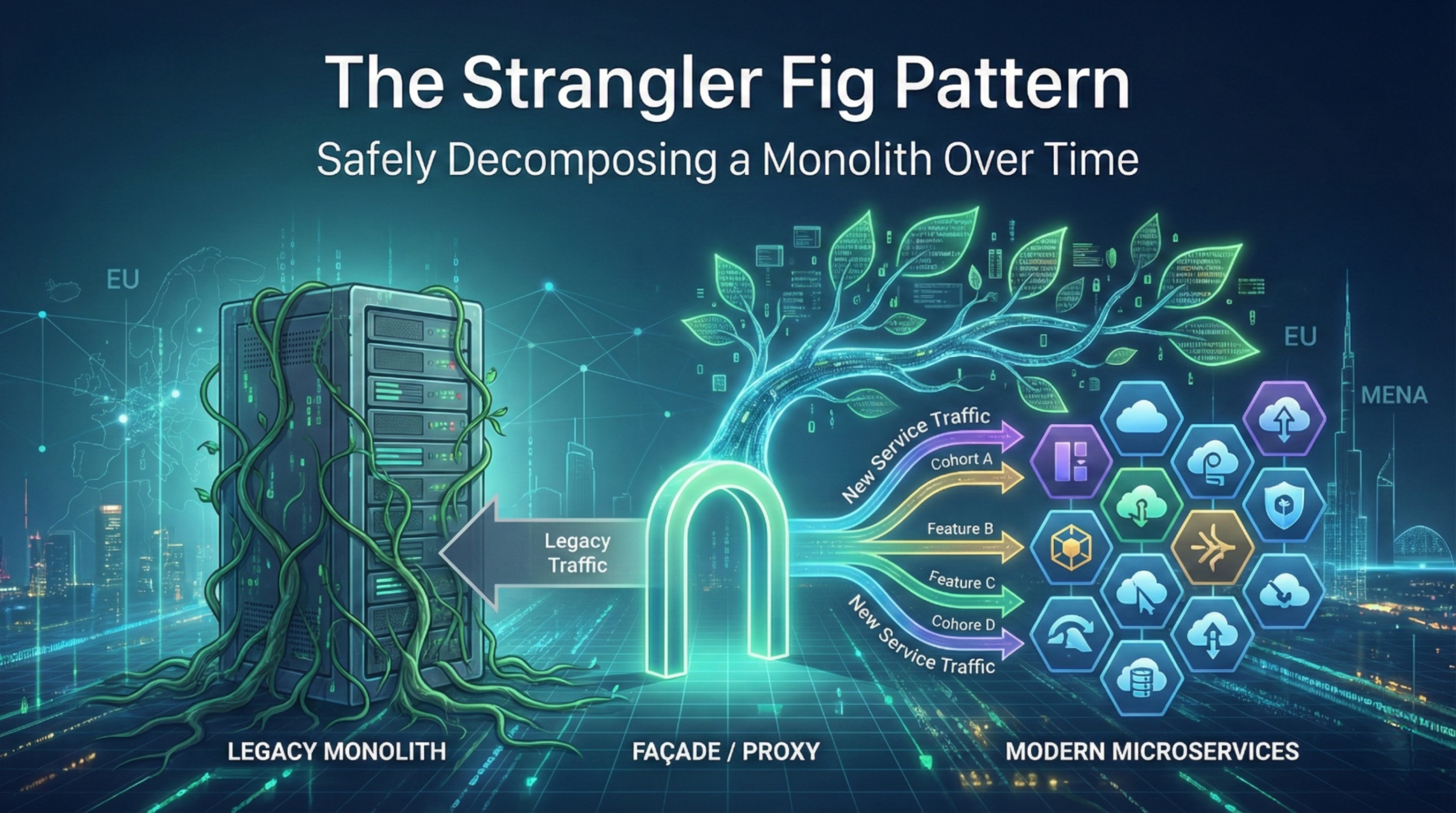
If your score supports moving beyond the monolith, treat migration as a staged investment. The default should be reversible steps.
Phased approach (a pragmatic path)
Phase 0: Baseline and stabilise
- Define current lead time, change failure rate, incident frequency, and unit costs.
- Clean up deployment pipeline, add observability, remove fragile manual steps.
Phase 1: Modularise inside the monolith
- Establish domain boundaries and code modules.
- Introduce API discipline internally, even before external services exist.
- Start cost allocation thinking now, not later.
Phase 2: Carve out one service that pays for itself
Pick a candidate with:
- clear business ownership
- independent scaling
- minimal shared database dependency
- measurable value such as reduced cycle time or improved SLO
Phase 3: Platform hardening
- Introduce paved road capabilities: templates, golden paths, secrets, policy checks, standard logging.
- Build shared reliability and security patterns so teams do not reinvent.
Phase 4: Expand selectively
- Expand only where the score remains strong.
- Retire old integration paths and manage technical debt aggressively.
Typical failure modes (what to watch for)
- Distributed monolith syndrome. Many services, but still a single release train and shared database.
- Governance overload. Too many approvals, teams cannot ship, so they create side paths.
- Tooling first, outcomes later. Investing in Kubernetes before defining SLOs and ownership.
- Cost surprise. More infrastructure, more environments, no cost attribution, then a budget shock.
- Security drift. Each team implements auth differently, incident response becomes slower.
Gartner’s warning about dissatisfaction by 2028 is often realised through these failure modes, not through the choice of architecture alone.
KPIs: how to measure value realisation
You need a scorecard that connects delivery performance to business outcomes.
Delivery and reliability:
- Deployment frequency and lead time for change
- Change failure rate and time to restore service
- SLO attainment and error budget burn rate
Economic:
- Unit cost per transaction, per workflow, or per active user
- Cloud cost variance to budget and cost per environment
- Cost of operational toil, measured in hours per week
Risk and compliance:
- Mean time to detect incidents
- Patch lead time for critical vulnerabilities
- Audit findings and remediation cycle time
For organisations under NIS2 and DORA style expectations, also measure incident reporting readiness and third party control coverage.
Anonymised example: MENA public sector service with seasonal spikes
A public service platform in MENA saw seasonal spikes tied to annual programmes. The monolith was stable but could not scale cost effectively for peak demand. They carved out a single high load eligibility calculation component behind an API gateway, then introduced event driven processing for asynchronous workflows. The outcome was improved peak resilience without turning the entire estate into microservices. This approach also made cost attribution clearer, which mattered because FinOps attention was increasing across the organisation.
Actionable Takeaways
- Treat the monolith vs microservices choice as an operating model change, not an architecture refresh.
- Score your context across volatility, scaling, team capacity, regulation, integration, security, and platform readiness before you commit.
- If you cannot fund platform guardrails and shared standards, prioritise a modular monolith and selective carve outs.
- Start with one service that pays for itself with measurable KPIs, then expand only if independence is real.
- Make data ownership explicit early, otherwise you will recreate monolith coupling with worse failure modes.
- Align security and resilience controls to regulatory expectations, even if you are not formally in scope today.
- Track value realisation using delivery, reliability, cost, and risk KPIs, not number of services shipped.
- Build FinOps into the programme from day one, because cloud cost pressure is already a top executive concern.
If you are assessing modernisation options for enterprise workflow automation and core business platforms, explore Averroa’s Enterprise Custom Development service and use it as a starting point for a decision workshop and implementation roadmap.
References
- CNCF Annual Survey 2024 report (March 2025).
- State of Cloud Native Development Q3 2025 for CNCF (October 2025).
- Flexera press release on 2025 State of the Cloud (March 19, 2025).
- Gartner press release on cloud trends (May 13, 2025).
- IBM Cost of a Data Breach Report 2024 (report covers March 2023 to February 2024, published July 2024).
- European Commission NIS2 policy page (includes transposition deadline and January 2026 amendments note).
- EIOPA DORA overview (entered into application 17 Jan 2025).
Should You Migrate at All? A Decision Framework for Monolith vs Microservices
“Move to microservices” has become a default recommendation in many enterprise roadmaps. In practice, the monolith vs microservices decision is not a style choice. It is a capital allocation decision with operational consequences. The timing matters because the external pressure is rising while delivery capacity is not. Cloud costs are climbing and cost governance is now front page for many CIOs. Flexera’s 2025 State of the Cloud release found 84% of organisations cite managing cloud spend as the top cloud challenge, with cloud spend expected to increase by 28% in the coming year. At the same time, regulators are tightening expectations on resilience and incident handling. The EU NIS2 transposition deadline was 17 October 2024, and the Commission is already proposing targeted amendments in January 2026 to simplify compliance. DORA entered into application on 17 January 2025 for financial entities.
Against that backdrop, microservices can be the right move, but only when the business context justifies the additional operating model, security, and platform overhead. This article gives a practical, executive friendly framework to decide, before you commit your organisation to a multi year migration.
Start with the real question: what problem are you trying to buy down?
A useful way to de risk the monolith vs microservices debate is to translate it into business problems you are willing to pay to solve. Microservices are not “better architecture”. They are a specific operating model for building and running software at scale.
In board terms, you pay for microservices with complexity, then you earn it back with speed, resilience, and organisational autonomy. If you cannot articulate where the payback shows up on your P and L or your risk register, the safest default is to improve the monolith.
Three signals that the “do nothing” option is getting more expensive:
- Cloud and platform economics are now a constraint. Flexera reports cloud spend is expected to rise 28% and budgets already exceed limits by 17% in many organisations. If you split a system into services without disciplined FinOps and platform standards, cost tends to sprawl rather than shrink.
- Security and resilience are becoming measurable obligations. IBM’s 2024 Cost of a Data Breach report put the global average breach cost at USD 4.88m, with the Middle East sample at USD 8.75m. Microservices change your attack surface, identity model, and incident blast radius. That can help or hurt, depending on governance.
- The market has normalised cloud native patterns. The CNCF Annual Survey (March 2025) reports 89% cloud native adoption, 91% of organisations using containers in production, and Kubernetes used, piloted, or evaluated by 93% of companies. In other words, the ecosystem is mature, but maturity does not remove the need for good judgement.
The decision framework below is designed to be used in portfolio governance, not as a technical beauty contest.
Monolith vs microservices: a decision framework you can score
I recommend a simple scoring model across seven dimensions. Use a 0 to 2 score for each. Total out of 14.
- 0 means monolith friendly
- 1 means ambiguous, proceed selectively
- 2 means microservices likely justified
1) Change volatility and release independence
Ask: do different parts of the system change at different rates, driven by different business owners?
A monolith is efficient when most changes are coordinated anyway. Microservices pay off when you have truly independent release trains. If every release still needs a cross domain steering committee, microservices will not produce speed, it will produce meetings.
Evidence context: microservices are widely adopted in the developer community, but adoption alone does not prove suitability. SlashData for CNCF (October 2025) reports microservices are used by 46% of backend developers and API gateways by 50%. Many of those implementations are supported by platform teams that hide complexity. If you do not have that platform maturity, independence is harder to achieve.
Score guidance:
- 0: mostly coordinated releases
- 1: some components could be independent
- 2: clear product domains with separate backlogs and KPIs
2) Scaling profile and performance hotspots
Ask: do you have uneven load, or a few services that need to scale differently?
Microservices make sense when scaling is asymmetric. If the whole system scales together, a well tuned monolith can be cheaper and simpler.
Score guidance:
- 0: uniform scaling, predictable load
- 1: a few hotspots, could be isolated with caching or modularisation
- 2: clearly separable workloads, spiky demand, different SLOs
3) Team topology and operational capacity
Ask: do you have the people to run distributed systems, not just build them?
This is where many programmes fail. Microservices require always on operational ownership, observability, SRE practices, and strong runbooks. Otherwise, you get a distributed monolith with slower delivery.
CNCF’s 2024 survey highlights containers in production are common, but deployment is “challenged primarily by cultural changes in the development team”. That cultural point is the real cost driver.
Score guidance:
- 0: one or two teams, limited 24 by 7 coverage
- 1: multiple teams, partial ownership, some on call maturity
- 2: several stable product teams, defined on call, incident process, platform support
4) Regulatory pressure and auditability
Ask: do you need stronger operational resilience, traceability, and third party controls?
For EU and many cross border firms, the baseline has moved. NIS2 required transposition by 17 October 2024 and repealed NIS1 from 18 October 2024. For financial entities, DORA entered into application on 17 January 2025 and explicitly covers ICT risk management, third party risk, resilience testing, and incident reporting.
Microservices can improve auditability if you standardise logging, identity, and change control. They can also create audit chaos if every team invents its own approach.
Score guidance:
- 0: minimal regulatory constraints
- 1: some compliance needs, manageable with monolith controls
- 2: high resilience and reporting expectations, complex third party ecosystem
5) Integration landscape and data ownership
Ask: are you integrating with many systems, and do you have a clear data model?
Microservices are a data architecture decision as much as an application decision. If you cannot define bounded contexts and data ownership, you will create distributed transactions, duplicated data, and inconsistent reporting.
Gartner warns that cloud adoption success is not guaranteed. It predicts 25% of organisations will experience significant dissatisfaction with cloud adoption by 2028 due to unrealistic expectations, suboptimal implementation, or uncontrolled costs. Integration and data sprawl are common root causes.
Score guidance:
- 0: simple integrations, single dominant data model
- 1: moderate complexity, needs API discipline
- 2: many systems, frequent integration change, strong need for domain boundaries
6) Security model and blast radius management
Ask: will microservices reduce or increase your risk?
IBM’s breach cost data is a reminder that the downside is material, especially in MENA where the 2024 Middle East average was USD 8.75m. Microservices can reduce blast radius if you enforce zero trust service identity, segmentation, and least privilege. They increase risk if you multiply endpoints without consistent controls.
Score guidance:
- 0: security controls are ad hoc today
- 1: some standardisation exists, gaps remain
- 2: strong IAM, secrets management, threat modelling, security testing pipelines
7) Platform and cost governance readiness
Ask: do you have a paved road?
Flexera reports 59% are expanding FinOps teams and 60% are using managed service providers to regain control of spend. That is not a coincidence. Microservices without FinOps and platform engineering is a fast route to cost surprises.
Score guidance:
- 0: no shared platform, limited observability, unclear cost allocation
- 1: partial platform, some shared tooling
- 2: internal developer platform or strong shared platform patterns, unit cost visibility
How to interpret the score
- 0 to 5: default to monolith improvement and modularisation
- 6 to 9: selective decomposition for the highest value domains
- 10 to 14: microservices can be justified, plan it as an operating model shift
What changes when you choose microservices: operating model, governance, and architecture
A monolith vs microservices decision changes how work moves through your organisation. Executives should ask for an explicit operating model plan, not just a target architecture diagram.
Operating model and governance changes
Key shifts:
- From project delivery to product ownership. Microservices work best when teams own services end to end, including run and improve.
- From central approvals to guardrails. Governance must move from manual gates to automated policy in pipelines, plus clear standards.
- From shared release management to service level accountability. Teams commit to SLOs and incident response, not just feature delivery.
Practical guardrails that prevent “microservices theatre”:
- Standard service templates (logging, metrics, tracing, health checks, security headers)
- Standard CI and CD patterns with mandatory checks
- Defined API lifecycle and versioning rules
- Centralised identity patterns for service to service access
- A clear exception process, measured and time boxed
Architecture and integration implications (systems, data, security)
Microservices raise three architectural obligations:
- API strategy becomes your integration contract. API gateways are popular for a reason. SlashData reports 50% of backend developers use API gateways. You need consistent routing, auth, throttling, and observability. Otherwise, consumers will break.
- Data must be owned, not shared casually. Shared databases recreate monolith coupling with worse failure modes. Prefer service owned schemas and event driven integration where it fits.
- Security must be uniform. Identity, secrets, encryption, and logging must be consistent. DORA’s focus on ICT risk management and third party oversight is a useful benchmark even outside finance.
Anonymised example: regulated EU group platform
A regulated EU group ran a core workflow platform that supported onboarding and case management. They wanted microservices because competitors were “moving faster”. A first scoring exercise showed only two domains had genuinely independent change cycles. The early win was not microservices. It was a modular monolith refactor plus a single carve out for the document processing domain, driven by scaling hotspots and vendor integration. That produced faster releases without expanding the audit scope across dozens of services.
Implementation approach: phases, guardrails, failure modes, and KPIs
If your score supports moving beyond the monolith, treat migration as a staged investment. The default should be reversible steps.
Phased approach (a pragmatic path)
Phase 0: Baseline and stabilise
- Define current lead time, change failure rate, incident frequency, and unit costs.
- Clean up deployment pipeline, add observability, remove fragile manual steps.
Phase 1: Modularise inside the monolith
- Establish domain boundaries and code modules.
- Introduce API discipline internally, even before external services exist.
- Start cost allocation thinking now, not later.
Phase 2: Carve out one service that pays for itself
Pick a candidate with:
- clear business ownership
- independent scaling
- minimal shared database dependency
- measurable value such as reduced cycle time or improved SLO
Phase 3: Platform hardening
- Introduce paved road capabilities: templates, golden paths, secrets, policy checks, standard logging.
- Build shared reliability and security patterns so teams do not reinvent.
Phase 4: Expand selectively
- Expand only where the score remains strong.
- Retire old integration paths and manage technical debt aggressively.
Typical failure modes (what to watch for)
- Distributed monolith syndrome. Many services, but still a single release train and shared database.
- Governance overload. Too many approvals, teams cannot ship, so they create side paths.
- Tooling first, outcomes later. Investing in Kubernetes before defining SLOs and ownership.
- Cost surprise. More infrastructure, more environments, no cost attribution, then a budget shock.
- Security drift. Each team implements auth differently, incident response becomes slower.
Gartner’s warning about dissatisfaction by 2028 is often realised through these failure modes, not through the choice of architecture alone.
KPIs: how to measure value realisation
You need a scorecard that connects delivery performance to business outcomes.
Delivery and reliability:
- Deployment frequency and lead time for change
- Change failure rate and time to restore service
- SLO attainment and error budget burn rate
Economic:
- Unit cost per transaction, per workflow, or per active user
- Cloud cost variance to budget and cost per environment
- Cost of operational toil, measured in hours per week
Risk and compliance:
- Mean time to detect incidents
- Patch lead time for critical vulnerabilities
- Audit findings and remediation cycle time
For organisations under NIS2 and DORA style expectations, also measure incident reporting readiness and third party control coverage.
Anonymised example: MENA public sector service with seasonal spikes
A public service platform in MENA saw seasonal spikes tied to annual programmes. The monolith was stable but could not scale cost effectively for peak demand. They carved out a single high load eligibility calculation component behind an API gateway, then introduced event driven processing for asynchronous workflows. The outcome was improved peak resilience without turning the entire estate into microservices. This approach also made cost attribution clearer, which mattered because FinOps attention was increasing across the organisation.
Actionable Takeaways
- Treat the monolith vs microservices choice as an operating model change, not an architecture refresh.
- Score your context across volatility, scaling, team capacity, regulation, integration, security, and platform readiness before you commit.
- If you cannot fund platform guardrails and shared standards, prioritise a modular monolith and selective carve outs.
- Start with one service that pays for itself with measurable KPIs, then expand only if independence is real.
- Make data ownership explicit early, otherwise you will recreate monolith coupling with worse failure modes.
- Align security and resilience controls to regulatory expectations, even if you are not formally in scope today.
- Track value realisation using delivery, reliability, cost, and risk KPIs, not number of services shipped.
- Build FinOps into the programme from day one, because cloud cost pressure is already a top executive concern.
If you are assessing modernisation options for enterprise workflow automation and core business platforms, explore Averroa’s Enterprise Custom Development service and use it as a starting point for a decision workshop and implementation roadmap.
References
- CNCF Annual Survey 2024 report (March 2025).
- State of Cloud Native Development Q3 2025 for CNCF (October 2025).
- Flexera press release on 2025 State of the Cloud (March 19, 2025).
- Gartner press release on cloud trends (May 13, 2025).
- IBM Cost of a Data Breach Report 2024 (report covers March 2023 to February 2024, published July 2024).
- European Commission NIS2 policy page (includes transposition deadline and January 2026 amendments note).
- EIOPA DORA overview (entered into application 17 Jan 2025).
Meet The Author
Meet The Author
Senior software engineer focused on backend systems and Android apps, delivering scalable web/mobile/cloud solutions. Leads technical direction, mentors teams, and ships high-performance services using ASP.NET Core/C#, microservices, and cloud-native infrastructure.
Senior software engineer focused on backend systems and Android apps, delivering scalable web/mobile/cloud solutions. Leads technical direction, mentors teams, and ships high-performance services using ASP.NET Core/C#, microservices, and cloud-native infrastructure.
Averroa Principal